Microsoft Azure is a great platform to host Virtual Machines. What native Azure doesn’t have is a good snapshot/checkpoint manager like Hyper-V does. Since some time now you can create disk snapshots per disk. If a Virtual Machine has multiple disks you have to create the snapshot for every disk. And for every disk it asks how you want to call it. Don’t even mention about putting the snapshot back in the VM.
That is where Azure Snapshot Manager comes in. This PowerShell based tool makes it a lot easier for you to create snapshots of all disks in one run. Also it allows you to apply the snapshot on any existing VM in the same region, but also create a new VM based of the selected snapshot. I have developed this script in a few iterations and I believe this version is ready to go into the wild.
If you have any suggestions or questions please check the About button on the site and let me know!
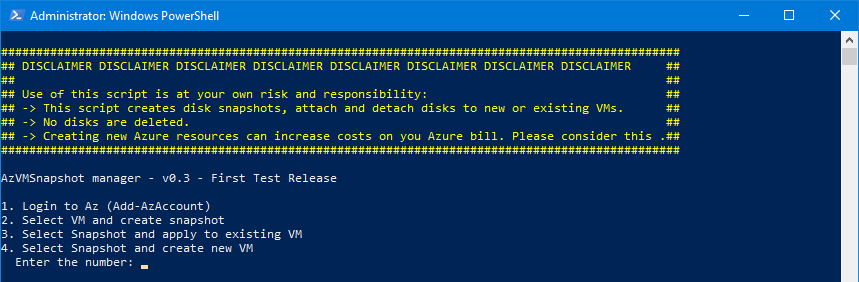
DISCLAIMER
Use of this script is at your own risk and responsibility: This script creates disk snapshots, attach and detach disks to new or existing VMs. No disks are deleted. Creating new Azure resources can increase costs on you Azure bill. Please take this into account.
DOWNLOAD
Download the script here: AzVMSnapshotMgr_v3.zip
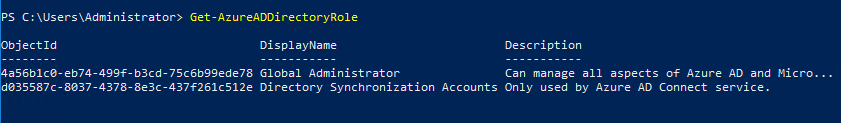
Start the script and connect to Azure.